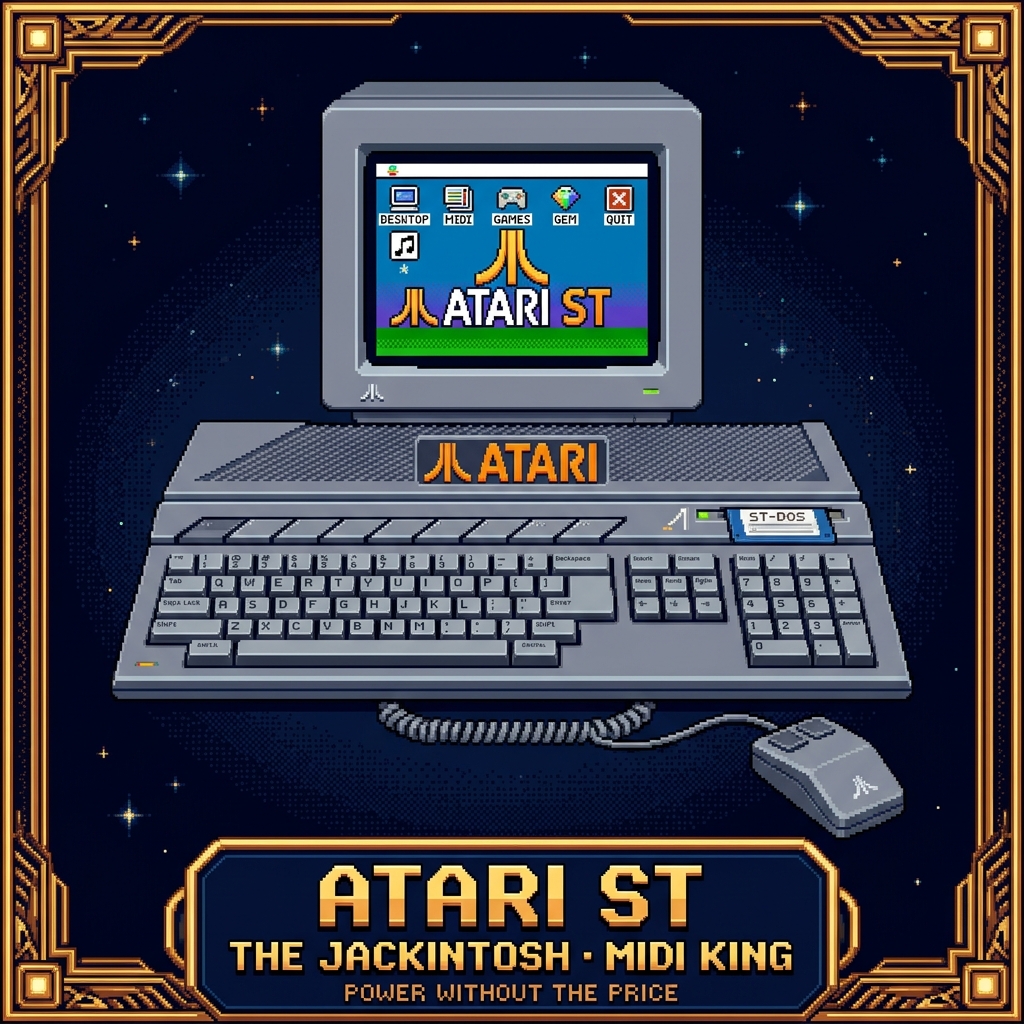
“Power without the price. The machine that brought the 16-bit graphical desktop to the masses.”
The Machine
Launched in 1985, the Atari ST (ST standing for Sixteen/Thirty-two, referencing the 68000's internal bus) was Atari's response to the 16-bit revolution. It was the first computer with a bitmapped color GUI integrated into its operating system (TOS/GEM) and the first to include built-in MIDI ports.
The "Jackintosh" moniker was a nod to both Jack Tramiel's aggressive pricing strategy and the machine's perceived rivalry with the Apple Macintosh. Tramiel, having left Commodore under acrimonious circumstances, acquired Atari and pushed for a machine that could under-cut the Macintosh while providing comparable graphical power.
The MIDI King
The Atari ST's most enduring legacy is its dominance in the music industry. By including MIDI (Musical Instrument Digital Interface) ports directly on the motherboard, Atari turned every ST into a professional sequencer. This decision alone ensured the machine's longevity long after its graphical capabilities were surpassed.
The hardware was remarkably stable for real-time MIDI processing, leading to the development of legendary software like C-Lab Creator (the ancestor of Logic Pro) and Cubase. For a decade, the Atari ST was the brain of virtually every professional recording studio and electronic music stage.
The GEM Desktop
The Graphics Environment Manager (GEM) provided a WIMP (Windows, Icons, Menus, Pointers) interface that felt familiar to Macintosh users but ran on significantly cheaper hardware. While the Macintosh was monochromatic at launch, the Atari ST offered color graphics and high-resolution monochrome options that were favored by desktop publishers and programmers.
The underlying TOS (The Operating System) was stored in ROM, meaning the machine booted almost instantly to the desktop — a sharp contrast to contemporary PCs that required floppy-disk loading for the OS.
The Architecture
While it lacked the highly specialized custom chips of its rival, the Commodore Amiga, the Atari ST relied on a fast Motorola 68000 CPU and a clean, straightforward memory map. Later models introduced the "Blitter" chip to accelerate graphical operations, but the machine's strength was always its balance of raw CPU speed and specialized I/O.
The ST's monochrome high-resolution mode (640x400) was exceptionally crisp for its time, making it a favorite for C development and MIDI sequencing where screen real estate and legibility were paramount.
The Atari ST didn't need to be the most complex machine; it needed to be the most accessible. By putting MIDI ports on a consumer computer, Atari accidentally created the foundation of modern electronic music.